CoinJar Security
From secure account access to institutional-grade asset custody, CoinJar's comprehensive security infrastructure protects your data, account, and digital assets with proven, multi-layered protection.

Built on trust and transparency

Account protection
Your account is protected with advanced encryption, regular security reviews, and proven security practices. Our systems automatically detect unusual login attempts, account breaches, and suspicious transactions to keep your funds safe.

Asset security
CoinJar protects 100% of customer assets using a combination of multi-signature wallets, multi-party computation (MPC) technology, and cold storage infrastructure. We maintain full reserves, so your cryptocurrency is always fully backed and available.

Trusted platform
CoinJar has operated globally for over a decade with a strong security record and reliable uptime. Our compliance-first, proactive approach includes proper licensing, robust security practices, and commitment to evolving regulatory standards worldwide.
Privacy
Your personal and financial information is stored and processed in cloud services that meet our strict infrastructure security requirements. For more information about the customer data we collect and how we use it, check out our Privacy Policy.
Infrastructure
CoinJar operates on Amazon Web Services, utilizing the same secure infrastructure trusted by governments and Fortune 500 companies worldwide for access control, end-to-end data encryption, continuous monitoring, and network isolation.
Your data is encrypted at all times, whether stored on our servers or transmitted between systems. We use zero trust security architecture, meaning every access request is verified regardless of source.
Our systems operate on private networks completely isolated from public internet access, with strict controls between our development and live environments. The most critical services are deployed on immutable operating systems that cannot be modified at runtime, ensuring consistent and tamper-proof infrastructure.
Company security
Every internal system requires multi-factor authentication for access. We follow strict access control policies with regular security reviews to ensure employees only have access to systems necessary for their role.
Every CoinJar employee undergoes comprehensive background verification before joining our team. All staff receive ongoing security training and anti-money laundering compliance education to maintain the highest standards of protection for your assets.
Outages and issues
Stay informed with our real-time Status page, which shows the current status of our wallets and services, details of any current incidents, and information about upcoming maintenance.
Bug bounty
Our Bug Bounty program engages ethical security researchers worldwide to help identify potential vulnerabilities. By rewarding responsible disclosure, we continuously strengthen our defenses and protect your assets.
Protecting your CoinJar

Protecting your CoinJar
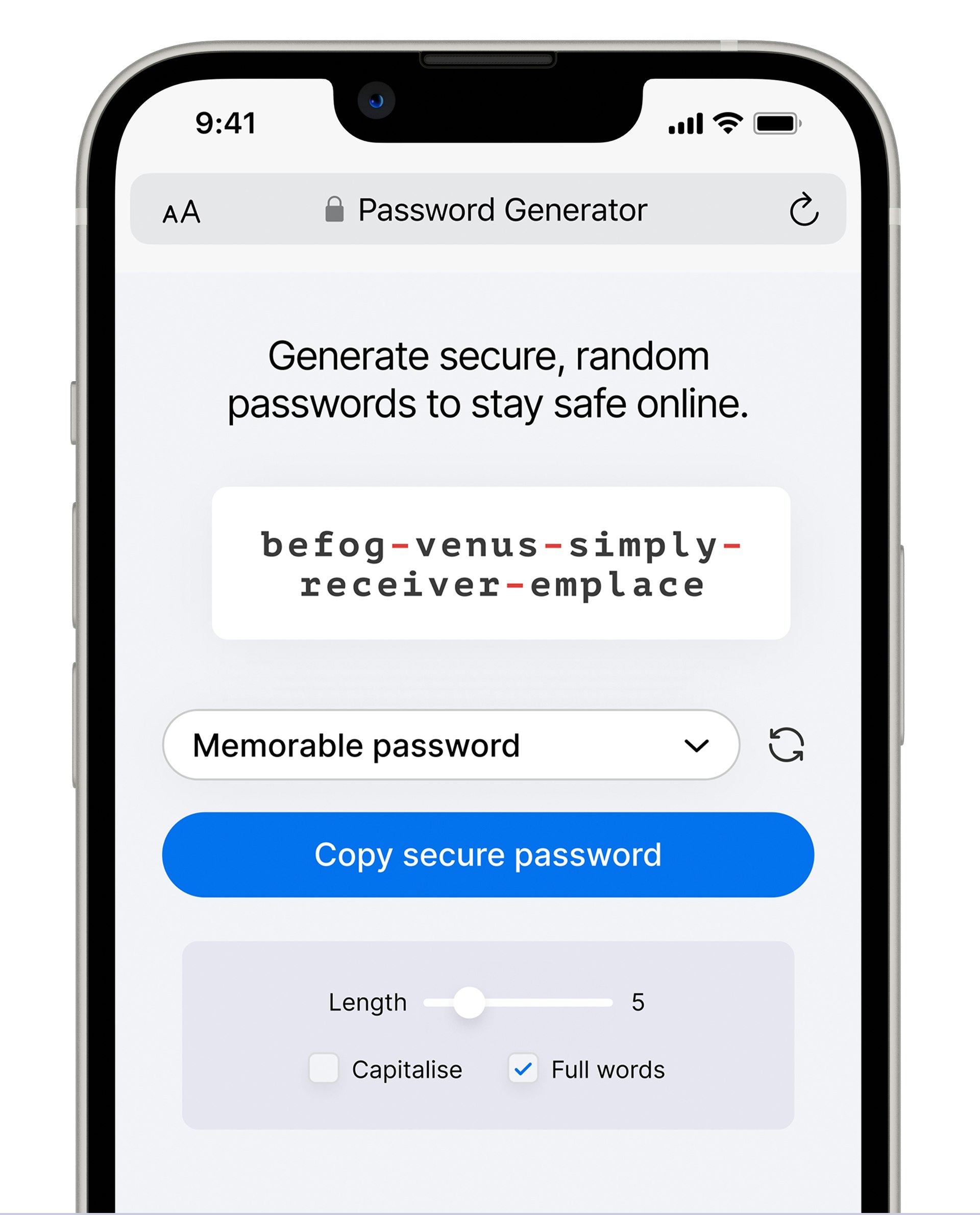
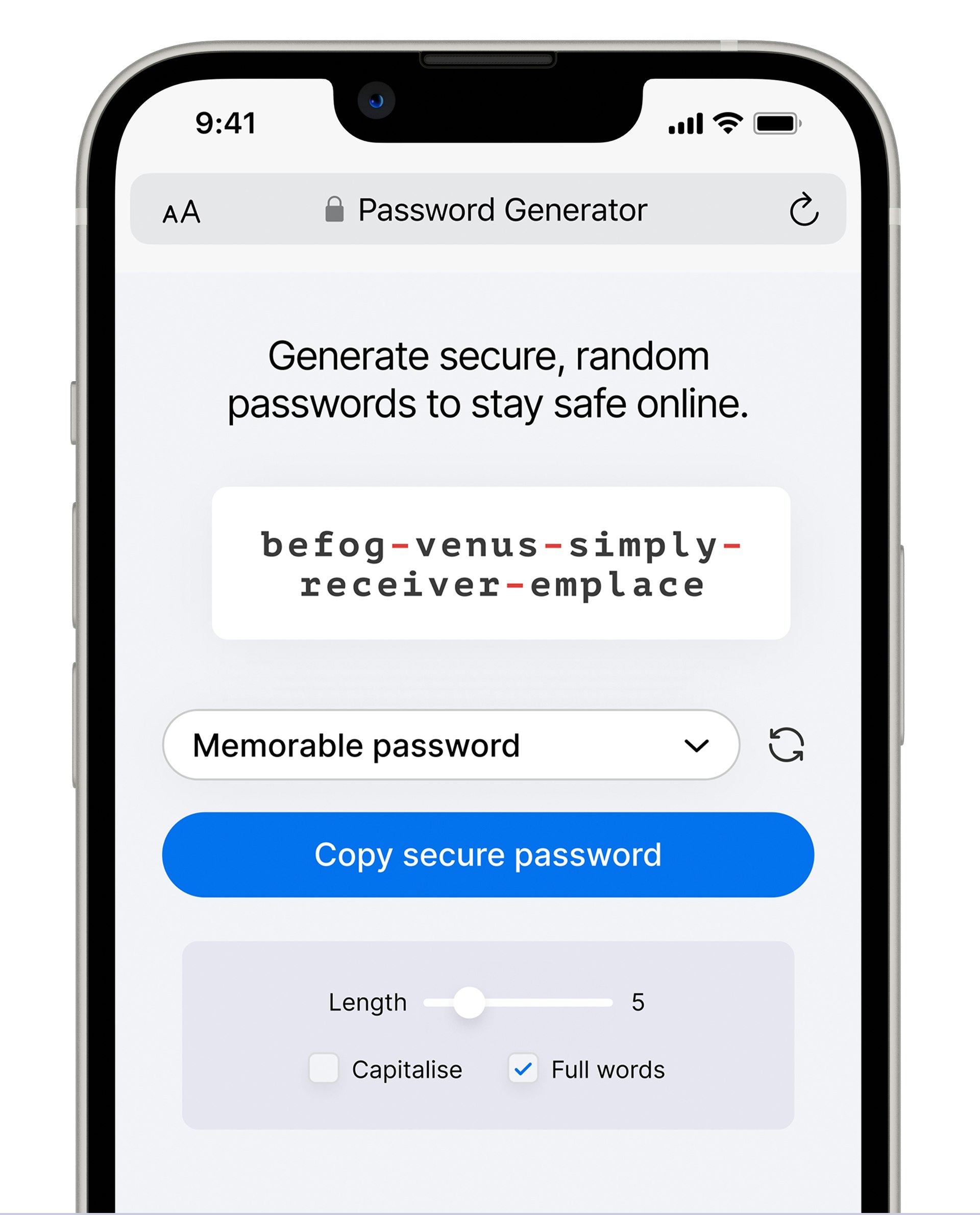
Pick a complex password
We recommend using a password manager like iCloud Keychain, Bitwarden or 1Password.